Inhoudsopgave
How to set up an OpenVPN server 2
Step 2 build certs and keys for server and client 2
How to set up a Linux OpenVPN client 6
Step 1 copy certificates and key files 6
How to set up an OS X OpenVPN client 7
OpenVPN How-to
Introduction
How to set up OpenVPN server with both Linux and Mac OS X clients
(A TechRepublic tip compilation)
October 2010
By Vincent Danen, modified by Henk Boschker on 20230830.
The three tips in this download were originally published individually in the Linux and Open Source blog and the Macs in Business blog on TechRepublic. Vincent Danen takes you through
the steps of setting up OpenVPN server and then how to set up both a Linux client and a Mac OS X client using Shimo.
How to set up an OpenVPN server
By Vincent Danen
Having a virtual private network affords a lot of convenience, particularly for those who want or need to access a remote network from a different location, such as connecting to a work network
from home, or vice versa. With the availability of 3G on the road, or wireless hotspots everywhere, being able to connect, securely, to a remote private network from anywhere is ideal.
OpenVPN is one of the most reliable VPN setups around. It's fully open source, it's supported on Linux, Windows, and OS X, it's robust, and it's secure. Unfortunately, configuration can be a bit
of a pain, so in a series of upcoming tips, I aim to get you up and running quickly.
To begin, you will need to have OpenVPN installed on the server or system you wish to use as a VPN end-point. Most distributions include OpenVPN; for the server setup, I am using OpenVPN
as provided by the OpenSUSE repository.
The first part of this series concentrates on the server, while the second and third parts will concentrate on the configuration of Linux and OS X clients, respectively. So without further ado,
let's get our hands dirty.
Step 1 download easy-rsa
To begin with, you need to install easy-rsa, not supplied by OpenSUSE, so download from the inernet.
Step 2 build certs and keys for server and client
# cd /etc/easy-rsa/
# vim vars
Step 6 RemainingIn the vars file, edit the KEY_* entries at the bottom of the file, such as KEY_COUNTRY, KEY_ORG, KEY_EMAIL, etc. These will be used to build the OpenSSL certificates. Next, it's
time to initialize the PKI:
# . ./vars
# sh easyrsa clean-all
# sh easyrsa init-pki or init-pki soft, to save variables.
# sh easyrsa build-ca
# sh easyrsa build-server-full server
For the above, and the below client certificates, you can enter pretty much anything for the "Common Name" field, however there is a certain logic to use: "OpenVPN-CA" when generating the Certificate Authority, "server" when generating the server certificate, and "client" or the name of the specific client system for the client certificates. Those certificates are generated with:
# sh easyrsa build-client-full client1
# sh easyrsa build-client-full client2
The next step is to generate the Diffie Hellman parameters for the server:
# sh easyrsa gen-dh
When this is done, you will have a number of files in the keys/ subdirectory. At this point, for the clients, you want to copy the appropriate files to them securely (i.e., via SSH or on a USB stick); the files the clients need are ca.crt, client1.crt, and client1.key (or whatever you named the files when you generated them with the build-key script).
Step 3 Configure server
Next, create the OpenVPN server configuration file. To get up and running quickly, copy one of the example config files:
# cd /etc/openvpn/
For extra security beyond that provided by SSL/TLS, create an "HMAC firewall" to help block DoS attacks and UDP port flooding.
Generate with:
# openvpn --genkey tls-auth ta.key
The server and each client must have a copy of this key.
The second parameter should be '0' on the server and '1' on the clients.
# cp /usr/share/doc/packages/openvpn/sample-config-files/server.conf .
# cp server.conf boschker.conf
# vi boschker.conf
The aim here is to get this going right away, so we won't examine each of the options in detail.
The primary things you want to do are to uncomment the "user" and "group" directives, to make the openvpn process run as the unprivileged "nobody" user. You may also want to change the "local" directive to make it listen to one specific IP address. This would be the IP to which your firewall is forwarding UDP port 1194. As well, you will want to set the "client-to-client"
directive to enable it, and also set the "push" directives for route and DNS options. What follows is a comment-stripped server.conf, as an example:
local 10.0.1.10
port 1194
proto udp
dev tun
ca ca.crt
cert boschker.crt
key boschker.key # This file should be kept secret
askpass vpnww.txt
dh dh.pem
server 10.0.2.0 255.255.255.0
ifconfig-pool-persist ipp.txt
push "route 10.0.1.0 255.255.255.0"
push "redirect-gateway def1 bypass-dhcp"
keepalive 10 120
tls-auth ta.key 0 # This file is secret
compress lz4-v2
push "compress lz4-v2"
user nobody
group nobody
persist-key
persist-tun
status /var/log/openvpn/openvpn-status.log
log-append /var/log/openvpn/openvpn.log
verb 3
explicit-exit-notify 1
Finally, copy the required keys and certificates that you previously generated:
# cd /etc/openvpn/
# cp /etc/easy-rsa/pki/ca.crt .
# cp /etc/easy-rsa/pki/issued/server.crt .
# cp /etc/easy-rsa/pki/private/server.key .
# cp /etc/easy-rsa/pki/dh.pem .
Step 5 Start server
And, finally, start the OpenVPN server:
# openvpn server or
# systemctl start
Step 6 Remaining
To get routing set up properly on the server so that remote clients, when they connect, can reach more than just the server itself, you will need to enable IP forwarding. This can be done by the following:
# echo 1 > /proc/sys/net/ipv4/ip_forward
You can also do it by editing /etc/sysctl.conf and adding the following (this is a good thing to do as it will ensure that packet-forwarding persists across reboots):
net.ipv4.ip_forward = 1
You also want to ensure that packets going back to the client system are routed properly. This can be done by changing the route on the gateway of the server's network to route packets to the
client network (10.8.0.1/32) through the OpenVPN server (if the server happens to be the gateway as well, you don't have to do anything additional to accomplish this). How this is done
largely depends on the operating system of the gateway.
Once this is done, you should be able to ping any machine on the server's LAN from the client, and be able to ping the client from any machine on the server's LAN. For instance, from a machine on the server LAN (not the server):
% traceroute 10.8.0.6
traceroute to 10.8.0.6 (10.8.0.6), 64 hops max, 52 byte packets
1 fw (192.168.10.1) 0.848 ms 0.342 ms 0.249 ms
2 server (192.168.10.11) 0.214 ms 0.231 ms 0.243 ms
3 server (192.168.10.11) 0.199 ms !Z 0.443 ms !Z 0.396 ms !Z
% ping 10.8.0.6
PING 10.8.0.6 (10.8.0.6): 56 data bytes
64 bytes from 10.8.0.6: icmp_seq=0 ttl=63 time=17.540 ms
And from the client:
# traceroute 192.168.10.65
traceroute to 192.168.10.65 (192.168.10.65), 30 hops max, 40 byte packets
1 10.8.0.1 (10.8.0.1) 22.963 ms 27.311 ms 27.317 ms
2 10.8.0.1 (10.8.0.1) 27.297 ms !X 27.294 ms !X 27.269 ms !X
# ping 192.168.10.65
PING 192.168.10.65 (192.168.10.65) 56(84) bytes of data.
64 bytes from 192.168.10.65: icmp_seq=1 ttl=62 time=515 ms
The setting up of OpenVPN clients will be the subject of two tips in the next week. I've made the assumption that the client is correctly configured here, simply to illustrate how it should look
when it all works together, but in the next parts of this series we will get into more depth with the client configuration.
How to set up a Linux OpenVPN client
By Vincent Danen modified by Henk Boschker on 2023-08-30.
In a previous tip last week, we looked at setting up an OpenVPN server. Now, I'll take you through the setup of a Linux OpenVPN client. (I have also covered setting up an OS X client on OpenVPN in the Macs in Business blog). The Linux client will be based on CentOS 5 using OpenVPN 2.0.9.
Step 1 copy certificates and key files
For each client, you will need to have copied the client's certificate and key, as well as the CA certificate, from the server. This should be done in a secure manner so you can ensure the files are not altered in any way, such as using SSH to transfer or a USB stick in your possession. Once they are on the client, copy them to the /etc/openvpn/ directory:
# cd /etc/openvpn
# cp ~/client.{key,crt} .
# cp ~/ca.crt .
Step 2 configure client
# cp /usr/share/doc/packages/openvpn/sample-config-files/client.conf .
# cp client.conf lappie-02.conf
# vi lappie-02.conf
In the lappie-02.conf, what you need to uncomment are the "user" and "group" directives, to make the openvpn run as the unprivileged" nobody" user rather than root. Also, if your key and
certificate files are not named "client.key" and "client.crt" you will need to change the crt and key directives in the file as well.
An uncommented client configuration file follows, that serves as an example:
client
dev tun
proto udp
remote 10.0.1.10 1194
nobind
group nobody
persist-key
persist-tun
mute-replay-warnings
ca ca.crt
cert lappie-02.crt
key lappie-02.key
askpass vpnww.txt
remote-cert-tls server
tls-auth ta.key 1
status /var/log/openvpn/openvpn-status.log
log-append /var/log/openvpn/openvpn.log
verb 4
Step 3 Start the VPN
To initiate a startup test, execute:
# openvpn client.conf or
# systemctl start
Step 4 test the VPN
See results of tracerout at the end of this writeing.
And finally, make sure it works:
# ping 10.8.0.1 -c 2
PING 10.8.0.1 (10.8.0.1) 56(84) bytes of data.
64 bytes from 10.8.0.1: icmp_seq=1 ttl=64 time=21.1 ms
64 bytes from 10.8.0.1: icmp_seq=2 ttl=64 time=14.8 ms
A connection to the remote OpenVPN server has been successfully established. And if you followed the previous tip about setting up the OpenVPN server, you should be able to ping and establish a connection to any other available system on the server's LAN at this point as well.
In order to access machines on the remote network with their FQDN (Fully Qualified Domain Name), you will need to modify /etc/resolv.conf to add a nameserver from the remote network to
the top of the list. This can, and probably should, be scripted so that the DNS server is used whenever the VPN connection is established. This will allow you to connect to "server.foo.com"
rather than always using IP addresses, like "192.168.10.23". On the server side, ensure that requests from this IP range (10.8.0.0/32) are not being blocked by the DNS server ACLs -- this is an important thing to remember, as it bit me and cost me a day of frustration.
At this point the Linux client is set up. The final part of this series (published in the Macs in Business blog on TechRepublic) shows you how to set up Shimo on OS X to connect to the
OpenVPN server and access the remote network's services.
How to set up an OS X OpenVPN client
In other tips I've covered how to set up an OpenVPN Linux server and an OpenVPN Linux client. Here, I look at setting up OpenVPN as a client on OS X.
There are a few possible clients to choose from. One popular OpenVPN client for OS X is Tunnelblick. Tunnelblick is free and open source. Another client is Viscosity. It has a cost of $9USD with a 30 day trial. Finally, my client of choice is Shimo, which is not just an OpenVPN client (like the other two), but also works with a number of other VPN and VPN-like solutions:
Cisco VPN, IPSec, PPTP/L2TP, SSH, and so forth. Shimo is more expensive than the others, but not by much: it is only €14.95 (about $21USD).
Shimo is also easy to use with OpenVPN. If you have followed along with the other OpenVPN tutorials in this series, you will have a copy of the client certificate, key, and the CA certificate on your system. If not, you will need to obtain them from the server, where they would have been generated, and securely copy (using SSH or a USB disk) them to your computer. Next, start Shimo and head to the Preferences. In the Profiles pane, add a new OpenVPN profile.

Under the General tab, name your new connection -- something like "OpenVPN Home" would suffice. In the Authentication pane, you will need to select your Certificate Authority file (ca.crt),
Local Certificate (client.crt), and Private Key File (client.key). Make sure the Authentication Method is set to Certificate (Figure A). There is no need to set the username and password unless it is required by the server (for the purposes of this series, we elected to use just certificates without further authentication mechanisms).
Figure A
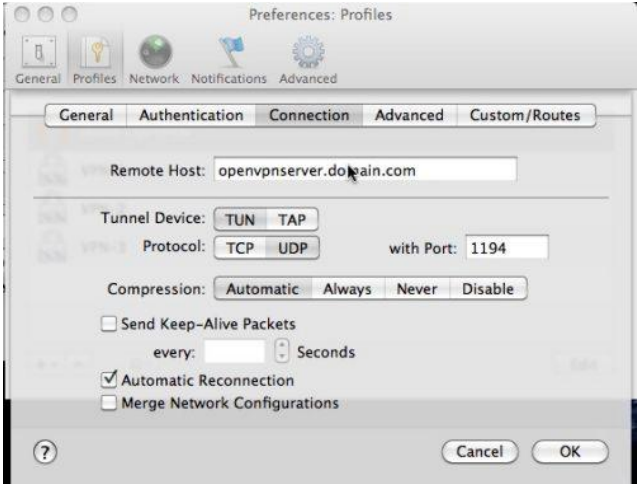
In the Connection tab, enter in the name of the remote host (i.e., openvpn-server.domain.com).
Ensure the Tunnel Device is TUN and the Protocol is UDP (Figure B); unless you have changed the connection port on the server, leave it at the default 1194. Set Compression to Automatic,
and enable Automatic Reconnection. You can also elect to send keep-alive packets every few seconds to ensure the connection stays up (i.e., maybe send a keep-alive packet ever 120 seconds
or so).
Figure B
That's it! You can save the preferences for this profile; go to the Shimo menu icon, and select the new OpenVPN network from the list, and Shimo will establish the connection. If you have enabled the OpenVPN server to push DNS and DNS domain information to clients, when you connect, you will be able to access systems on the remote network by their computer names directly rather than IP addresses.
If you have an iPhone, you're in for an even bigger treat. With iPhone tethering, you can be on the road, anywhere, and securely access the home or work network simply by connecting your iPhone to the laptop (via USB or Bluetooth) and enabling tethering on the iPhone (via Settings | General | Network | Internet Tethering). Once the connection between the Mac and iPhone is established, simply fire up Shimo or whatever OpenVPN client you have chosen, and establish the VPN connection. This works so well that I have been able to obtain a kerberos-ticket and access a kerberos-authentication-only web site on the internal network while sitting in my car across town.
If you only need to use OpenVPN, Shimo may be overkill. It is a fantastic and robust OpenVPN client, but you may wish to give something like Tunnelblick a go first to see if it meets your
needs. The latest version of Tunnelblick is 3.0, but it requires you to edit the OpenVPN client configuration directly.
This makes it a lightweight frontend to the OpenVPN command-line program, and the configuration for such can be found in the previous tip about configuring the Linux client.
Primarily, you will need to change the "remote" directive to point to the OpenVPN server, and ensure that the ca, cert, and key directives are correct. These directives look for those files in the directory that the configuration file resides in, so you will want to copy those files to ~/Library/Application Support/Tunnelblick/Configurations/.
Once that is done and the configuration file has been saved, use the Tunnelblick menu icon to initiate a connection to the specified OpenVPN server and watch the OpenVPN log output as it
connects.
There are a few options to establishing connections to OpenVPN on the Mac. Tunnelblick is good, if a little rough. It is, after all, a simple frontend to the openvpn command line program.
Shimo is great if you need a little more power, flexibility, and hand-holding. It is also the best of the bunch if you need to connect to different types of VPNs.
Zonder VPN
lappie-02:/etc/openvpn # dig nn.nl
; <<>> DiG 9.16.42 <<>> nn.nl
;; global options: +cmd
;; Got answer:
;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 13889
;; flags: qr rd ra ad; QUERY: 1, ANSWER: 2, AUTHORITY: 0, ADDITIONAL: 1
;; OPT PSEUDOSECTION:
; EDNS: version: 0, flags:; udp: 1232
; COOKIE: dc60fd1523210f140100000064ef0aab091a0def0dce87a0 (good)
;; QUESTION SECTION:
;nn.nl. IN A
;; ANSWER SECTION:
nn.nl. 20 IN A 23.32.248.186
nn.nl. 20 IN A 23.3.104.104
;; Query time: 275 msec
;; SERVER: fdf6:5834:5519:1000::10#53(fdf6:5834:5519:1000::10)
;; WHEN: Wed Aug 30 11:23:55 CEST 2023
;; MSG SIZE rcvd: 94
lappie-02:/etc/openvpn # ping nn.nl
PING nn.nl (23.32.248.186) 56(84) bytes of data.
64 bytes from a23-32-248-186.deploy.static.akamaitechnologies.com (23.32.248.186): icmp_seq=1 ttl=50 time=282 ms
64 bytes from a23-32-248-186.deploy.static.akamaitechnologies.com (23.32.248.186): icmp_seq=2 ttl=50 time=282 ms
64 bytes from a23-32-248-186.deploy.static.akamaitechnologies.com (23.32.248.186): icmp_seq=3 ttl=50 time=282 ms
64 bytes from a23-32-248-186.deploy.static.akamaitechnologies.com (23.32.248.186): icmp_seq=4 ttl=50 time=282 ms
^C
--- nn.nl ping statistics ---
4 packets transmitted, 4 received, 0% packet loss, time 3001ms
rtt min/avg/max/mdev = 281.521/281.727/281.932/0.149 ms
lappie-02:/etc/openvpn # traceroute nn.nl
traceroute to nn.nl (23.32.248.186), 30 hops max, 60 byte packets
1 gallery.thuis.local (10.0.1.10) 0.245 ms 0.213 ms 0.214 ms
2 192.168.2.254 (192.168.2.254) 0.847 ms 0.866 ms 0.854 ms
3 static.kpn.net (195.190.228.54) 3.645 ms 3.605 ms 3.671 ms
4 * * *
5 * * *
6 nl-ams17b-rc1-lag-105-0.aorta.net (84.116.130.65) 167.303 ms 166.612 ms 166.638 ms
7 us-was03a-rd1-ae-105-0.aorta.net (84.116.130.66) 166.248 ms 165.596 ms 165.546 ms
8 us-nyc01b-rd2-ae-5-0.aorta.net (84.116.146.141) 99.723 ms 99.728 ms 99.564 ms
9 us-sjo01a-ri3-ae-18-0.aorta.net (84.116.146.33) 166.967 ms 166.148 ms 166.881 ms
10 124.215.192.53 (124.215.192.53) 165.696 ms 165.852 ms 164.703 ms
11 pajbb001.int-gw.kddi.ne.jp (111.87.3.125) 165.665 ms 164.760 ms pajbb001.int-gw.kddi.ne.jp (111.87.3.121) 166.887 ms
12 106.187.13.29 (106.187.13.29) 279.525 ms 106.187.13.45 (106.187.13.45) 265.875 ms 106.187.13.5 (106.187.13.5) 274.642 ms
13 27.85.199.2 (27.85.199.2) 271.996 ms 27.85.199.6 (27.85.199.6) 271.453 ms 27.86.44.226 (27.86.44.226) 268.917 ms
14 111.87.18.54 (111.87.18.54) 338.432 ms 338.065 ms 337.717 ms
15 a23-32-248-186.deploy.static.akamaitechnologies.com (23.32.248.186) 272.729 ms 274.091 ms 272.722 ms
lappie-02:/etc/openvpn #
Active VPN
lappie-02:/etc/openvpn # dig nn.nl
; <<>> DiG 9.16.42 <<>> nn.nl
;; global options: +cmd
;; Got answer:
;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 43539
;; flags: qr rd ra ad; QUERY: 1, ANSWER: 2, AUTHORITY: 0, ADDITIONAL: 1
;; OPT PSEUDOSECTION:
; EDNS: version: 0, flags:; udp: 1232
; COOKIE: 85a49847bf4950790100000064eeff707935d92d0948c378 (good)
;; QUESTION SECTION:
;nn.nl. IN A
;; ANSWER SECTION:
nn.nl. 20 IN A 2.16.165.155
nn.nl. 20 IN A 2.16.165.90
;; Query time: 39 msec
;; SERVER: fdf6:5834:5519:1000::10#53(fdf6:5834:5519:1000::10)
;; WHEN: Wed Aug 30 10:36:00 CEST 2023
;; MSG SIZE rcvd: 94
lappie-02:/etc/openvpn # ping nn.nl
PING nn.nl (2.16.165.90) 56(84) bytes of data.
64 bytes from a2-16-165-90.deploy.static.akamaitechnologies.com (2.16.165.90): icmp_seq=1 ttl=52 time=20.8 ms
64 bytes from a2-16-165-90.deploy.static.akamaitechnologies.com (2.16.165.90): icmp_seq=2 ttl=52 time=21.4 ms
64 bytes from a2-16-165-90.deploy.static.akamaitechnologies.com (2.16.165.90): icmp_seq=3 ttl=52 time=20.2 ms
64 bytes from a2-16-165-90.deploy.static.akamaitechnologies.com (2.16.165.90): icmp_seq=4 ttl=52 time=22.6 ms
64 bytes from a2-16-165-90.deploy.static.akamaitechnologies.com (2.16.165.90): icmp_seq=5 ttl=52 time=22.5 ms
64 bytes from a2-16-165-90.deploy.static.akamaitechnologies.com (2.16.165.90): icmp_seq=6 ttl=52 time=21.0 ms
64 bytes from a2-16-165-90.deploy.static.akamaitechnologies.com (2.16.165.90): icmp_seq=7 ttl=52 time=18.8 ms
^C
--- nn.nl ping statistics ---
7 packets transmitted, 7 received, 0% packet loss, time 6011ms
rtt min/avg/max/mdev = 18.823/21.045/22.568/1.217 ms
lappie-02:/etc/openvpn # traceroute nn.nl
traceroute to nn.nl (95.101.23.200), 30 hops max, 60 byte packets
1 10.0.2.1 (10.0.2.1) 5.492 ms 6.089 ms 5.849 ms
2 192.168.2.254 (192.168.2.254) 5.619 ms 5.387 ms 5.262 ms
3 static.kpn.net (195.190.228.54) 6.948 ms 7.296 ms 7.489 ms
4 * * *
5 * * *
6 ae-9.r21.amstnl07.nl.bb.gin.ntt.net (129.250.2.232) 9.804 ms 5.983 ms 7.818 ms
7 ae-17.r21.frnkge13.de.bb.gin.ntt.net (129.250.3.76) 12.504 ms 12.037 ms 11.370 ms
8 213.46.184.103 (213.46.184.103) 31.316 ms 31.784 ms 31.719 ms
9 a95-101-23-200.deploy.static.akamaitechnologies.com (95.101.23.200) 30.664 ms 31.328 ms 31.217 ms
lappie-02:/etc/openvpn #







